Linux Suspicious ELF File Static Analysis Techniques and Approaches
Background: Sometimes during daily cases we see suspicious detections on Linux machines which have hashes that do not exist on popular platforms and we do not have licenses for sandboxes. To resolve these challenges we need to be able to analyze malware for Linux using in-house solutions only.
Preparation:
To prepare for it, we need to prepare our sandbox. To use it, take any virtualization technology solution, then prepare the OS. For that reason, we need to use FreeBSD, which comes with all the necessary tools that come with this operating system.
Malware static analyze: In our example, we shall use an approach to analyze ELF files, which are Linux/Unix native executable binaries. In this article, we shall look into static analysis of ELF files and will try to figure out what the main components are where we need to take a look to reveal the approximate activity which will be done by the ELF file after execution, and of course understand the components where we should focus and the toolsets that will provide us capability without additional installation to work with the file.
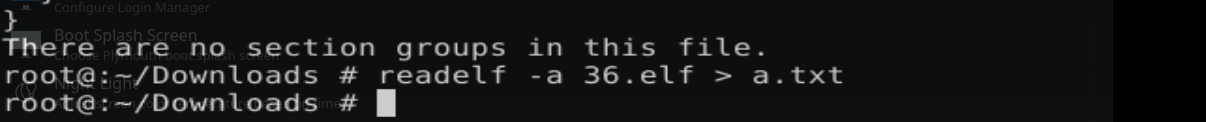
Step 1 (Find useful section header): As I have mentioned, for a starting point we need FreeBSD. We shall use the "readelf" package to read the ELF file. And one of the sections is .rodata (Read-Only data), which purpose is to store immutable and other critical data which can be used by ELF logic. .data mutable config data (e.g., flags, counters, or partially decrypted payloads).
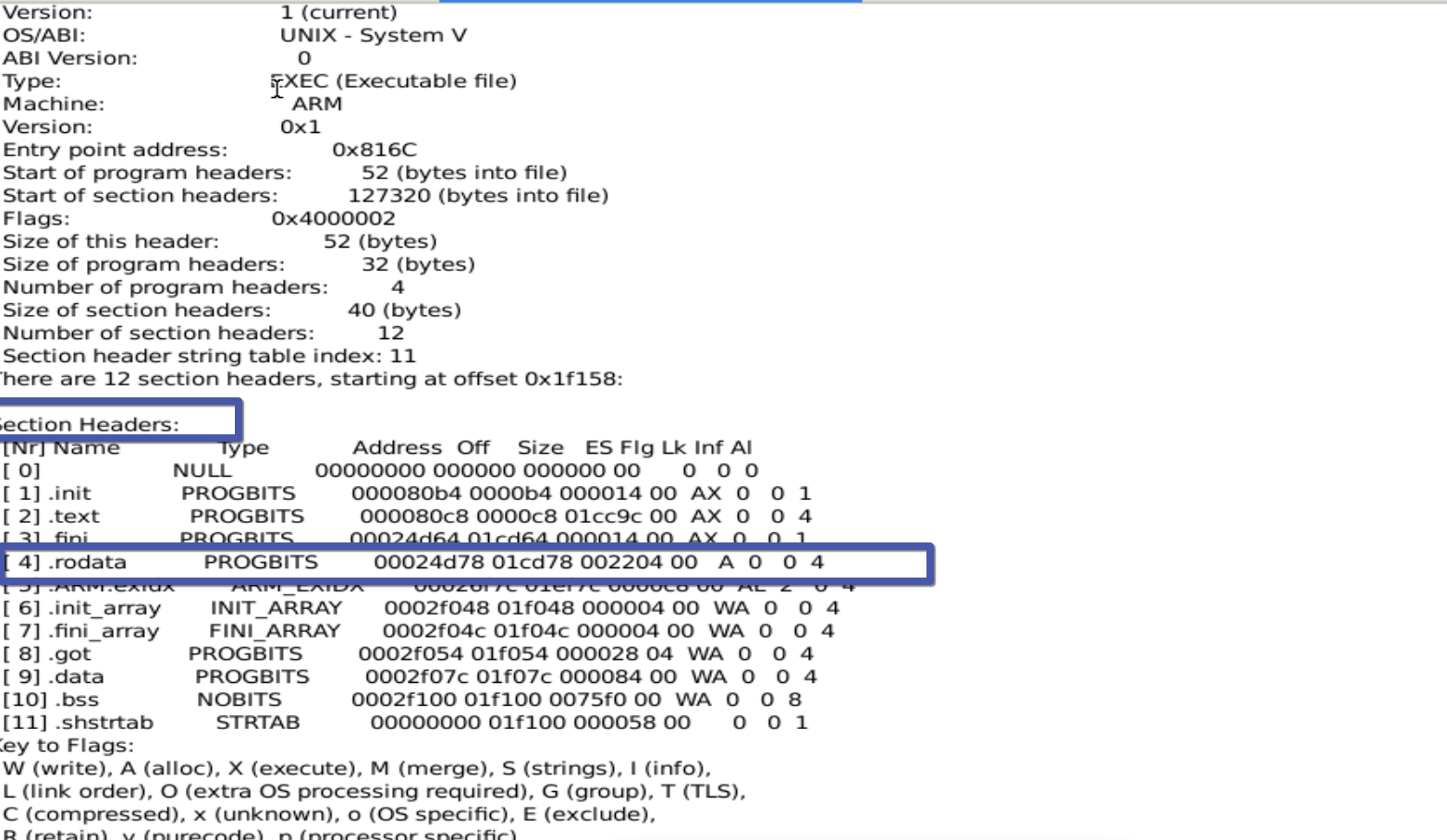
Step 2 (Discover IOC): Before discovery, we need to extract the header sections via "readelf -x HEADERSECTIONNAME Filename" (replace HEADERSECTIONNAME with the specific section name, such as .data or another header section), and as a result, we can see a lot of IoCs from this ELF file, like IoT devices, user agent information, and so on.
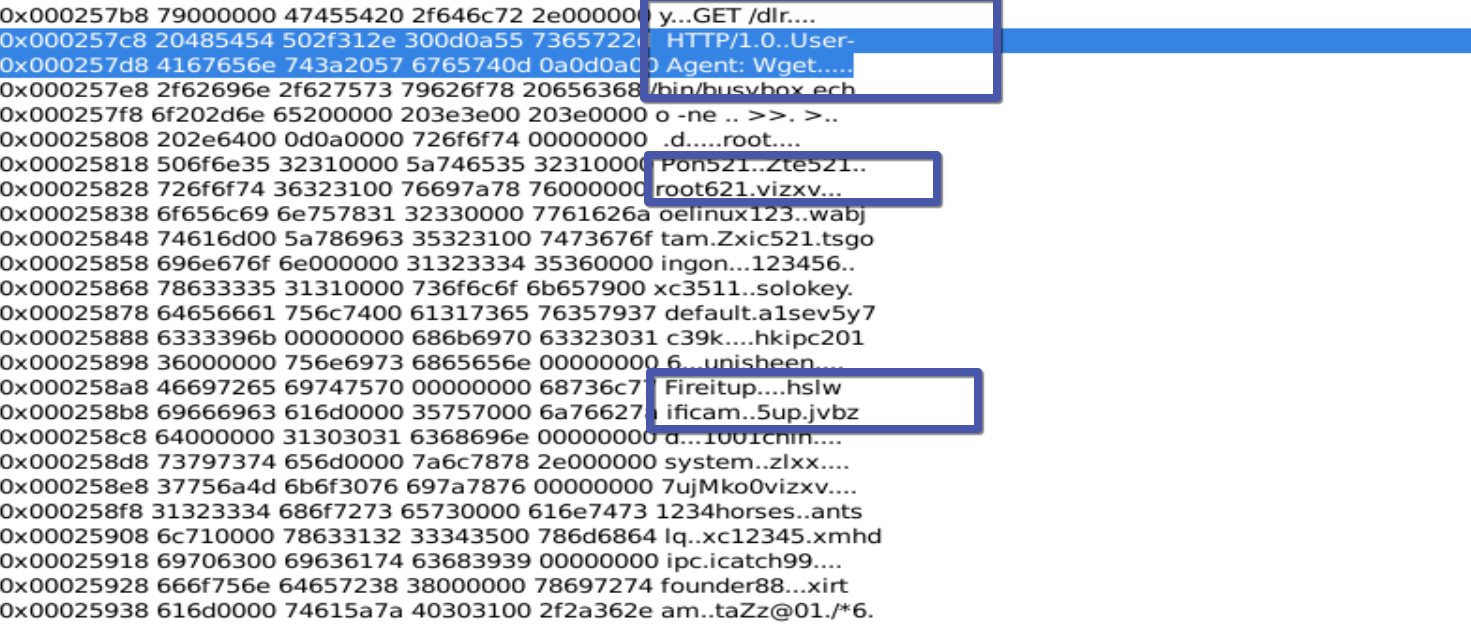
Conclusion: Sometimes, extracting header sections is a useful action to understand the IoCs and sometimes some of the behavior of the ELF file, which is sometimes one of the fastest ways to understand the impact on your environment if, for some reasons, your incidents involved ELF malware.
